We were never supposed to ever know anything about the following, yet, here it is…be careful who you share this with.

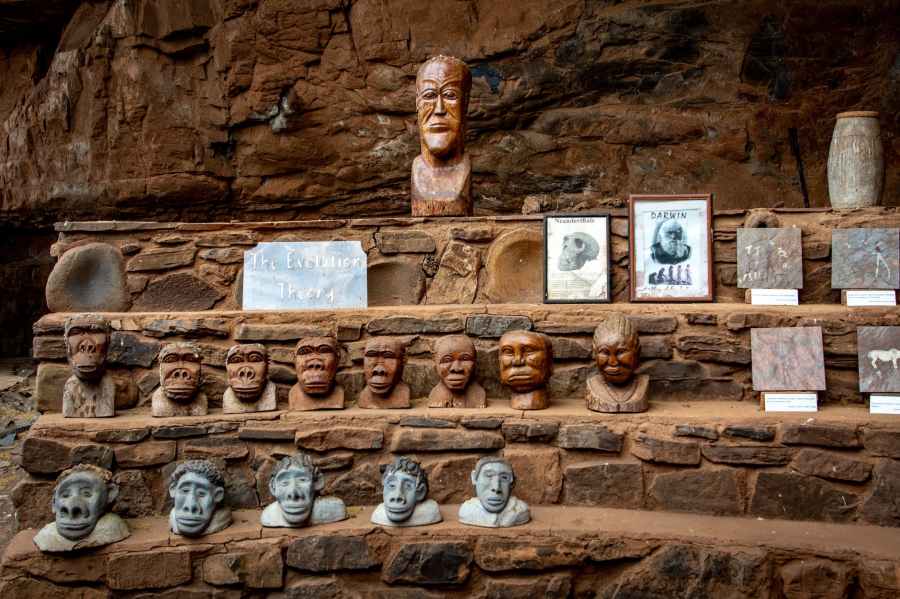
The DARWIN semiconductor chip is a major technological breakthrough that will give the United States a significant advantage in the global economy. China, of course, would love to get its hands on this technology, and it would be willing to do whatever it takes to acquire it. And this has come about thru advanced usage of Government’s Extremely Intelligent AI. But China will want this one for sure.
Here are some possible scenarios of how China could try to get the DARWIN chip:
- Cyberattacks. China could launch cyberattacks on the American companies that are developing the DARWIN chip. These attacks could be designed to steal the chip’s design or to disrupt its production.
- Economic coercion. China could use its economic power to pressure the United States to give up the DARWIN chip. For example, China could threaten to impose tariffs on American goods or to stop buying American debt.
- Espionage. China could send spies to infiltrate the American companies that are developing the DARWIN chip. These spies could try to steal the chip’s design or to recruit employees to defect to China.
- Direct action. China could even try to steal the DARWIN chip by force. For example, Chinese operatives could try to steal the chip’s design from an American company or to sabotage its production facilities.
The United States would need to take steps to protect the DARWIN chip from these threats. These steps could include strengthening cybersecurity, increasing economic sanctions against China, and improving intelligence gathering. The United States would also need to work with its allies to deter China from taking any aggressive actions.
The race to develop the DARWIN chip is a major geostrategic competition between the United States and China. The outcome of this competition will have a significant impact on the future of the global economy and on the balance of power in the world. But America has actually designed a new AI assisted semiconductor Chip called DARWIN. The possibilities with such a chip are phenomenal.
The possibilities with a DARWIN chip are truly phenomenal. Here are just a few of the things that this chip could enable:
- Artificial intelligence (AI): The DARWIN chip could be used to create even more powerful AI systems. These systems could be used to solve complex problems in areas such as healthcare, transportation, and manufacturing.
- Virtual reality (VR) and augmented reality (AR): The DARWIN chip could be used to create more immersive VR and AR experiences. These experiences could be used for entertainment, education, and training.
- Self-driving cars: The DARWIN chip could be used to power self-driving cars. These cars would be able to navigate the road safely and efficiently without human input. Boats and Planes could also become self flying and self correcting and navigating on the Seas. Military Planes could takeoff, fly a Mission like into a highly Radioactive Zone and return and land. Planes like a B-1 Bomber and so on.
- Robotics: The DARWIN chip could be used to create more advanced robots. These robots could be used for a variety of tasks, such as manufacturing, healthcare, and customer service.
- Healthcare: The DARWIN chip could be used to develop new medical devices and treatments. These devices and treatments could help to diagnose and treat diseases more effectively.
- Energy: The DARWIN chip could be used to develop more efficient energy technologies. These technologies could help to reduce our reliance on fossil fuels and combat climate change.
These are just a few of the possibilities that the DARWIN chip could enable. As AI and other technologies continue to develop, we can only imagine the amazing things that this chip will make possible.
In addition to the possibilities listed above, the DARWIN chip could also be used to:
- Develop new forms of encryption that are more secure than anything that exists today.
- Create new forms of entertainment that are more immersive and realistic than anything that we have ever experienced before.
- Design new ways to educate people that are more effective and engaging.
- Improve the efficiency of our transportation systems, making it easier and faster to get around.
- Revolutionize the way that we work, making it possible for us to do our jobs from anywhere in the world.
The DARWIN chip is truly a game-changer, and it has the potential to change the world in many ways. We can only imagine what the future holds for this technology.
Espionage?
types of espionage that might be used:
- Human intelligence (HUMINT): This is the most traditional form of espionage, and involves gathering information from people who have access to it. This can be done through a variety of means, such as recruiting spies, planting informants, or conducting surveillance.
- Signals intelligence (SIGINT): This involves collecting and analyzing electronic signals, such as radio, telephone, and satellite communications. This can be done by intercepting the signals themselves, or by analyzing the metadata associated with them.
- Imagery intelligence (IMINT): This involves collecting and analyzing images, such as those taken by satellites, aircraft, or ground-based cameras. This can be used to identify targets, track movements, or assess damage.
- Technical intelligence (TECHINT): This involves collecting and analyzing technical data, such as that related to weapons systems, computer networks, or industrial processes. This can be used to understand the capabilities of an adversary, or to develop countermeasures.
- Open-source intelligence (OSINT): This involves collecting and analyzing publicly available information, such as news reports, social media posts, and government documents. This can be a valuable source of information, as it can provide insights into an adversary’s intentions, capabilities, and vulnerabilities.
These are just a few of the many types of espionage that might be used by China. The specific methods used will vary depending on the target, the information being sought, and the resources available.
In addition to these traditional types of espionage, there are also a number of newer methods that are becoming increasingly common. These include:
- Cyber espionage: This involves using computers and networks to steal information or disrupt operations.
- Economic espionage: This involves stealing trade secrets or other sensitive information that could be used to give an organization a competitive advantage.
- Biomedical espionage: This involves stealing or disrupting research and development in the biomedical field.
These newer methods of espionage are often more difficult to detect and prevent, and they can have a significant impact on the target. As a result, they are becoming increasingly popular among both state and non-state actors. 🇨🇳 may soon be sending in more Agents to America to search for the DARWIN technologies.
And they could get them because of LAX Security measures at some Technology Banks.
Spies use a variety of techniques to trick people into giving up information. Some of these techniques include:
- Building rapport. Spies will often try to build rapport with their target in order to gain their trust. They may do this by sharing personal information about themselves, or by being sympathetic to the target’s problems.
- Using flattery. Spies may also use flattery to get their target to open up to them. They may compliment the target’s appearance, intelligence, or accomplishments.
- Playing on the target’s emotions. Spies may try to play on the target’s emotions in order to get them to reveal information. They may do this by making the target feel scared, guilty, or sympathetic.
- Using deception. Spies may lie to their targets in order to get them to believe something that is not true. They may also use false documents or other forms of deception to trick their targets.
- Using technology. Spies may use technology to trick their targets. This could include using hidden cameras or microphones, or using social media to track their targets’ movements.
Spies are also trained in the art of observation. They can quickly assess a person’s body language and facial expressions to determine if they are telling the truth. They can also use their knowledge of human psychology to manipulate people into revealing information.
It is important to be aware of the techniques that spies use to trick people. If you are ever approached by someone who seems to be trying to get information from you, be careful about what you say. Trust your instincts and don’t be afraid to walk away if you feel uncomfortable.
Here are some additional tips for avoiding being tricked by spies:
- Be aware of your surroundings. If you are in a public place, be aware of who is around you and what they are doing.
- Don’t give out personal information. This includes your name, address, phone number, or any other information that could be used to identify you.
- Be careful about what you say online. Anything you post online can be seen by anyone, including spies.
- Trust your gut. If you feel uncomfortable about someone or something, don’t be afraid to walk away.
By following these tips, you can help to protect yourself from being tricked by spies.
China has been involved in stealing a wide range of technology from the United States, including:
- Military technology. China has been accused of stealing information on U.S. weapons systems, including the Patriot missile system, the F-35 Joint Strike Fighter, and the U.S. Navy’s new Littoral combat ship.
- Commercial technology. China has been accused of stealing information on a wide range of commercial technologies, including medical devices, semiconductors, and software.
- Intellectual property. China has been accused of stealing intellectual property from U.S. companies, including trade secrets, patents, and trademarks.
The extent of China’s technology theft is difficult to quantify, but it is estimated to cost the U.S. economy billions of dollars each year. The theft of technology can have a number of negative consequences, including:
- It can give China an unfair advantage in the global marketplace.
- It can stifle innovation in the United States.
- It can lead to job losses in the United States.
The U.S. government has taken a number of steps to try to combat China’s technology theft, including:
- Imposing sanctions on Chinese companies and individuals involved in the theft of technology.
- Prosecuting Chinese hackers who steal technology from U.S. companies.
- Working with allies to share information about China’s technology theft.
However, the challenge of combating China’s technology theft is significant. China has a vast intelligence apparatus and a sophisticated cyberwarfare capability. The U.S. government will need to continue to take aggressive action to protect its technology from China’s theft.
In addition to the specific technologies listed above, China has also been accused of stealing more general knowledge and know-how from the United States. This includes information on how to design and manufacture products, how to conduct research and development, and how to manage businesses. This stolen knowledge can give China a significant advantage in the global economy.
The theft of technology from the United States is a serious problem that has the potential to harm the U.S. economy and national security. The U.S. government needs to take aggressive action to combat this problem, and businesses need to be vigilant in protecting their intellectual property.
MIP.Many are ignorant about Intellectual Properties. Let’s Review-
Intellectual property (IP) is a broad term that encompasses a variety of creations of the mind, such as inventions, literary and artistic works, and symbols, names, and images used in commerce. IP can be protected by patents, copyrights, trademarks, and trade secrets.
China has been accused of stealing IP from U.S. companies in a variety of ways, including:
- Cyberattacks. Chinese hackers have been accused of hacking into the computer systems of U.S. companies to steal IP.
- Economic espionage. Chinese spies have been accused of using traditional espionage techniques, such as cultivating sources and conducting surveillance, to steal IP from U.S. companies.
- Forced technology transfer. Chinese companies have been accused of forcing U.S. companies to share IP as a condition of doing business in China.
- Copycatting. Chinese companies have been accused of copying the products and designs of U.S. companies without permission.
The theft of IP from U.S. companies can have a number of negative consequences, including:
- It can give Chinese companies an unfair advantage in the global marketplace.
- It can stifle innovation in the United States.
- It can lead to job losses in the United States.
The U.S. government has taken a number of steps to try to combat China’s IP theft, including:
- Imposing sanctions on Chinese companies and individuals involved in the theft of IP.
- Prosecuting Chinese hackers who steal IP from U.S. companies.
- Working with allies to share information about China’s IP theft.
However, the challenge of combating China’s IP theft is significant. China has a vast intelligence apparatus and a sophisticated cyberwarfare capability. The U.S. government will need to continue to take aggressive action to protect its IP from China’s theft.
In addition to the specific techniques listed above, China has also been accused of using more subtle methods to steal IP from U.S. companies. For example, Chinese companies have been known to hire former U.S. employees who have access to IP, or to send employees to the United States to attend conferences and trade shows in order to gather information.
The theft of IP from U.S. companies is a serious problem that has the potential to harm the U.S. economy and national security. The U.S. government needs to take aggressive action to combat this problem, and businesses need to be vigilant in protecting their IP.
China has a vast intelligence apparatus, which is made up of a number of different agencies. The most important of these agencies is the Ministry of State Security (MSS), which is responsible for all of China’s external intelligence gathering. The MSS has a large budget and employs a large number of people, including both civilian and military personnel.
Other important intelligence agencies in China include the Ministry of Public Security (MPS), which is responsible for domestic security, and the People’s Liberation Army (PLA), which has its own intelligence arm. The MPS has a large network of informants and surveillance capabilities, while the PLA has a strong cyberwarfare capability.
China’s intelligence apparatus is used to gather information on a wide range of topics, including:
- The military capabilities of other countries.
- The political and economic situation in other countries.
- The activities of foreign companies and organizations.
- The activities of Chinese citizens abroad.
China’s intelligence apparatus is also used to conduct economic espionage, which is the theft of trade secrets and other confidential information from foreign companies. China’s intelligence apparatus is considered to be one of the most sophisticated in the world, and it is a major threat to the security of other countries.
Here are some of the capabilities of China’s intelligence apparatus:
- Cyberwarfare: China has a strong cyberwarfare capability, and it has been accused of hacking into the computer systems of foreign companies and governments.
- Economic espionage: China has been accused of conducting economic espionage against foreign companies, in order to steal trade secrets and other confidential information.
- Human intelligence: China has a large network of informants and agents around the world, who gather information for the intelligence apparatus.
- Technical intelligence: China has a sophisticated technical intelligence capability, which includes the use of satellites, drones, and other sensors to gather information.
China’s intelligence apparatus is a major threat to the security of other countries. It is important for countries to be aware of the capabilities of China’s intelligence apparatus, and to take steps to protect themselves from its activities.
China’s Espionage Apparatus has expanded ten fold in the last six years and Billion of Dollars (China spent $224.2 billion on its intelligence services in 2020) now Budgeted toward these Activities by the Chinese Government. And the Senate Members have been studying China’s new espionage apparatuses. But another big concern?
However, there is evidence to suggest that Russia and China do share some espionage secrets. For example, in 2016, the U.S. Department of Justice charged a Russian hacker with stealing military secrets from the U.S. and sharing them with China. Additionally, in 2018, a report by Team 29, a Russian lawyers watchdog group, noted that China has been implicated in 17 cases of this kind over the past two decades.
It is important to note that not all espionage secrets are shared between Russia and China. For example, the U.S. intelligence community believes that Russia has not shared its most sensitive military secrets with China. However, it is possible that Russia and China share some less sensitive secrets, such as information about foreign companies or governments.
The sharing of espionage secrets between Russia and China is a serious concern for the United States and its allies. It allows these countries to gain an advantage in the global intelligence arena, and it could also lead to the sharing of sensitive military secrets. The U.S. government is working to counter this threat by increasing cooperation with its allies and by improving its own intelligence capabilities.
Sources
thumb_upthumb_downtuneshareGoogle itmore_vert
Search related topics
search Does Russia trade acquired espionage secrets with chinasearch Who is the Russian scientist spying for China?search What happened to the Russian spy exchanged for powers?add_circle
The exact amount that Russia, China, and America spend on their intelligence gathering apparatuses is classified information. However, there are estimates available that give us a general idea of the scale of spending.
According to the Stockholm International Peace Research Institute (SIPRI), Russia spent $64.2 billion on its intelligence services in 2020. This is the second-highest level of spending in the world, after the United States. China spent $224.2 billion on its intelligence services in 2020, which is the highest level of spending in the world. The United States spent $80.4 billion on its intelligence services in 2020, which is the third-highest level of spending in the world.
It is important to note that these estimates are just that – estimates. The actual amount that these countries spend on their intelligence services is likely higher than these estimates.
The high level of spending on intelligence gathering reflects the importance that these countries place on intelligence. Intelligence is essential for these countries to maintain their national security and to protect their interests in the global arena.
The high level of spending on intelligence gathering also reflects the increasingly complex and competitive world that we live in. In this world, intelligence is essential for countries to stay ahead of the curve and to make informed decisions about their security and their future.

You must be logged in to post a comment.